Chrome Update July 14, 2020:
- As of today, Chrome is restoring SameSite enforcement. It coincides with the release of Chrome v84, but is being enforced on Chrome v80+ as per the original rollout policy. Make sure your site & analytics implementation is compatible.
Chrome Update April 3, 2020:
- Chrome has rolled back SameSite enforcement indefinitely in light of the global disruption from COVID-19.
Updated February 11, 2020:
- Added link to drop-in solution for all cookies set via JavaScript.
Updated February 3, 2020:
- Google previously indicated that SameSite would be shipped with Chrome v80 on February 4, 2020, but is now saying that these updates will go live "for an initial limited population starting the week of February 17, 2020."
- Previously, we indicated that the upcoming SameSite updates would have no impact on Google Analytics tracking. However Simo Ahava pointed out that cross-iframe tracking for cross-site iframes can be affected -- we've added instructions for handling those cases as a result.
PSA: The upcoming #SameSite enforcement in Google Chrome v80 (Feb 4) *can* impact your first-party analytics trackers.
If you load content from a cross-site host in an iframe, any JS cookies being accessed within that iframe would need SameSite=None;Secure settings. #measure
— Simo Ahava (@SimoAhava) January 31, 2020
What is the SameSite Update?
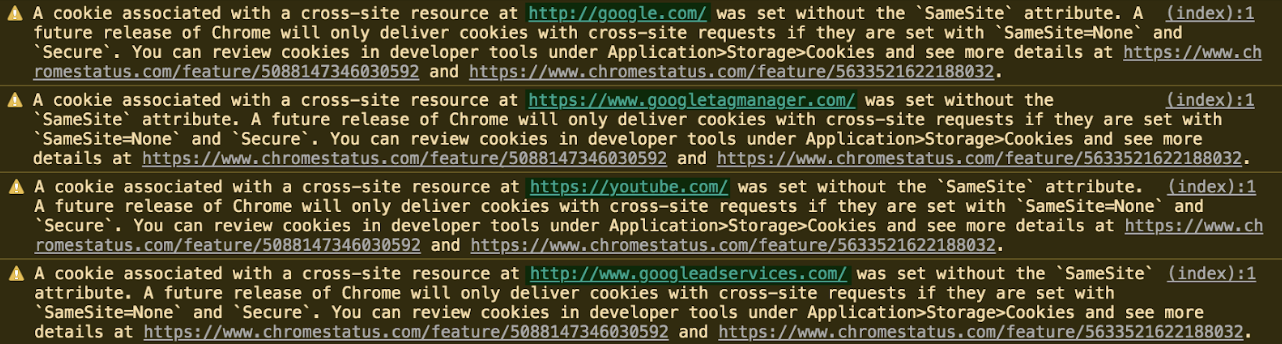
Last year Google announced an update to cross-site cookie standards as part of an ongoing effort to improve data privacy and security. The new standards go live the week of February 17th, 2020. Firefox and Edge have support planned, but no ETA.
These changes means that cross-site (a.k.a. third-party) cookies must explicitly declare themselves as cross-site (details) and use HTTPS exclusively (details).
Industry Impact of SameSite
The SameSite update, on its own, does not impose any new restrictions. The only direct effects of this are:
- a healthy dose of overconcern from dev-adjacent folks
- a small bit of research for all web developers, and minor code updates for some
- a shedding of old unused third-party cookies, saving marginal bytes of bandwidth across the internet-verse
SameSite adds zero functional benefit (or obstacles) on its own, but will be a foothold for more impactful updates. The first of which concerns security and is arriving simultaneously…
By requiring cross-site / third-party cookies to be encrypted, some hacker attack vectors are negated (e.g. CSRF). It's yet another move by Google to push the percentage of the web on HTTPS even higher. And moving to HTTPS is always a win for platform security and user privacy!
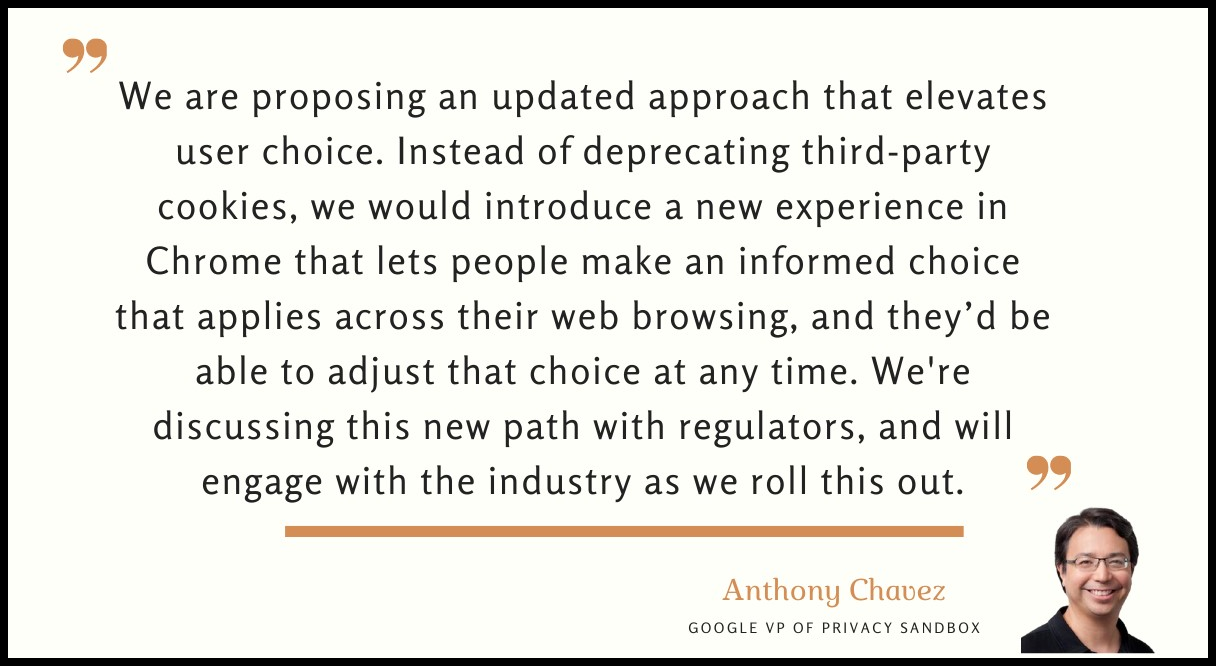
I'd wager the SameSite cookie attribute will also be a stepping stone for future changes from Chromium's Privacy Sandbox, which seems to be the thoughtful and diverse approach needed (*cough* ITP) to protect users while also enabling providers.
Some Things Will Break
If all goes well, end-users won't see any changes from the SameSite updates. But in reality, we may run into a hiccup or two in our everyday tools as end-users ourselves. There will surely be services, scripts, features, and plugins that are less actively maintained that will break, partially or entirely. And there's always the chance of a major provider fudging their update!
As an end-user, if something breaks on February 17th or soon after:
- Clear your cookies and retry.
- Inform the provider.
- If you don't want to wait for the provider to roll out a fix, you can "fix" it for yourself by disabling the new SameSite cookie restriction in Chrome: chrome://flags/#same-site-by-default-cookies (Not a long-term solution, but can be handy in a pinch to get that website widget or browser extension or Trello power-up working again!)
As a provider, read on to make sure your applications don't break for your users!
Are You Ready for SameSite?
Most third-party cookie usage are third-party tracking or authentication platforms. Do not worry about those, because those vendors will make the necessary changes on their end, if they haven't already.
Will SameSite Impact Google Analytics?
This SameSite update only affects third-party cookies, so generally should NOT affect Google Analytics or any other platforms that use only first-party tracking cookies. However, there is one exception: cross-site iframes.
Cross-site iframes are inherently a third-party context to the page, and so SameSite could break any cross-iframe tracking you have in place. We're hoping Google will update analytics.js so Universal Analytics tracking will continue to work within iframes as it did before the SameSite updates, but:
- It's not guaranteed Google will update analytics.js, so it may be prudent to implement a custom workaround.
- Tracking in iframes that are not on HTTPS can break, even if analytics.js is automatically updated by Google.
- Older versions of GA tracking, including ga.js, will almost certainly not get updated by Google. If you have non-Universal GA tracking in an iframe, it's liable to break will need to be updated.
- With any updates, iframe tracking on the initially-loaded iframe page may continue to track as expected, but tracking after the iframe reloads (e.g. on form confirmation pages inside iframes) may not have access to tracking cookies set on the initial iframe page. This means that tracking will have a different GA client id, and will not have access to any cookies set on the initial iframe page.
If you rely on cross-iframe tracking for measurement, you'll need to make changes to be in compliance with the SameSite updates. Otherwise, your Google Analytics tracking should not be affected.
How to Preview SameSite Functionality
First, confirm whether your browser is already enforcing the SameSite updates by visiting this site. If all rows are green, then these updates are already being enforced. If not, then you can test the behavior of your cookies in third-party contexts with the new restrictions in Chrome by enabling two feature flags: chrome://flags/#same-site-by-default-cookies and chrome://flags/#cookies-without-same-site-must-be-secure.
How to Prepare for SameSite
SameSite cookie requirements will start being enforced on a widespread basis starting the week of February 17th, 2020. If your application uses third-party cookies, you'll need to prepare by:
- Set
SameSite=Nonewhen setting any third-party cookie (details). - Set
Securefor any third-party cookie. This means, if you're using any non-HTTPS URLs in conjunction with third-party cookies, you'll need to migrate those to HTTPS (details).
Google has a full rundown for developers, a great overview video, and a detailed testing guide from the Chromium team. This deep dive from Auth0 is a great resource as well.
GA Tracking in Cross-Site Iframes
The one area where SameSite could break your GA tracking is cross-site iframes. If your iframes are on the same top-level domain as the contained page, or you have no cross-iframe tracking in place, then nothing will change. But if you have cross-site iframes with cross-iframe tracking in place, then you'll want to update your setup.
Common cross-iframe tracking solutions should continue to function as expected in cases where no navigation/reloading happens within the iframe, but we recommend updating your setup just to be safe.
- Firstly, iframes have to be on HTTPS.
- There are multiple methods for making the main GA cookie compatible with SameSite. Adding this code to customTask for all GA hits in iframes is the simplest and most versatile approach. See the tip in the previous section for an alternative method that covers all JS cookies.
- Lastly, you should update all custom cookies that are read or set within iframes to be set with
SameSite=None; Secure.
What If, Worst Case?
Theoretically, if both you and your ad/analytics platform vendor failed to make the necessary updates for SameSite, then for Chrome users:
- Conversions might not be tracked in some or all cases, if the tracking relied on cross-site cookies. But chances are good there are fallbacks, so likely impact on conversion reporting would still be minimal to none.
- Specific analytics features that rely on third-party cookie-ing (such as GA's demographics reports), would flatline.
- Remarketing / ad targeting would break.
- Tracking in cross-site would break sessions and not be connected to users' behavior outside of iframes.
But if you trust the vendor (which, of course you do, or else they would not be your vendor!), then trust them to be prepared for a seamless transition. If you have concern for any particular vendor, contact the vendor directly for more information.
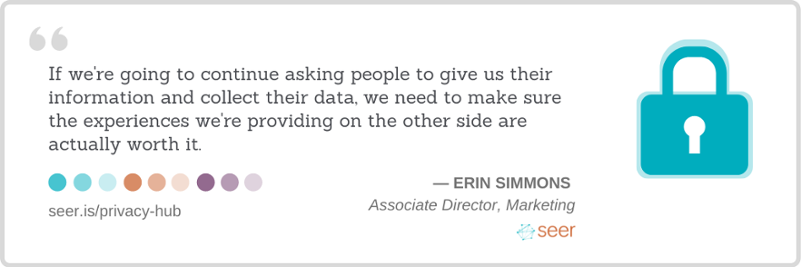
Our team at Seer will continue to keep you updated on the latest news in digital marketing. We'll report back on the impact of SameSite over the developing months. In the meantime, check out some of the other recent updates rocking the industry:
- January 2020 Core Algorithm Update
- November 2019 Google Ads Close Variant Update
- November 2019 Google Ads Conversion Bug
Sign up for our newsletter for more posts like this - delivered straight to your inbox!